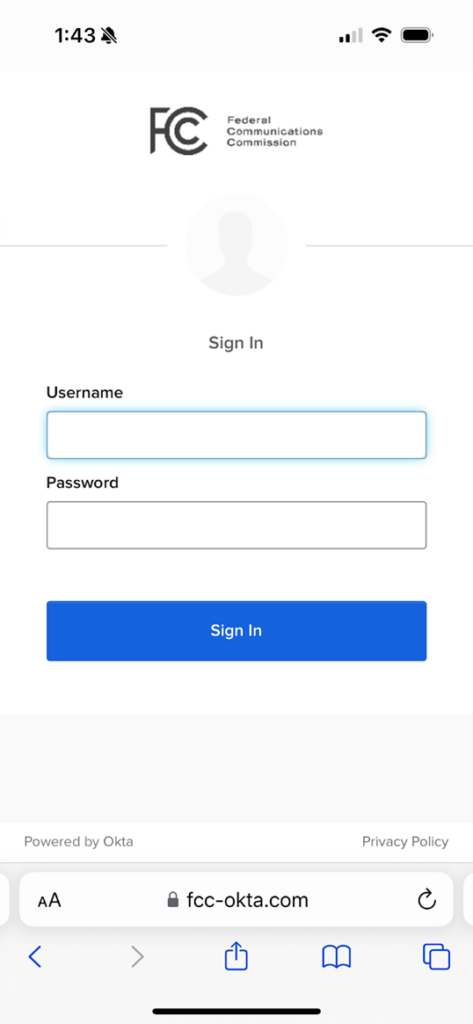
The Federal Communications Commission (FCC) has fallen victim to a cunning phishing campaign, alongside various cryptocurrency platforms, according to recent discoveries by security researchers at Lookout. The attack uses fake Okta single sign-on (SSO) pages in a strategy to deceive users into disclosing confidential information.
Criminals are targeting hundreds of people, mostly in the US, with identical techniques to get photo IDs and password reset URLs.
Phishing attacks are becoming increasingly common, and the targets of these attacks include users of well-known platforms such as Okta, Gmail, iCloud, Outlook, Twitter, Yahoo, and AOL.
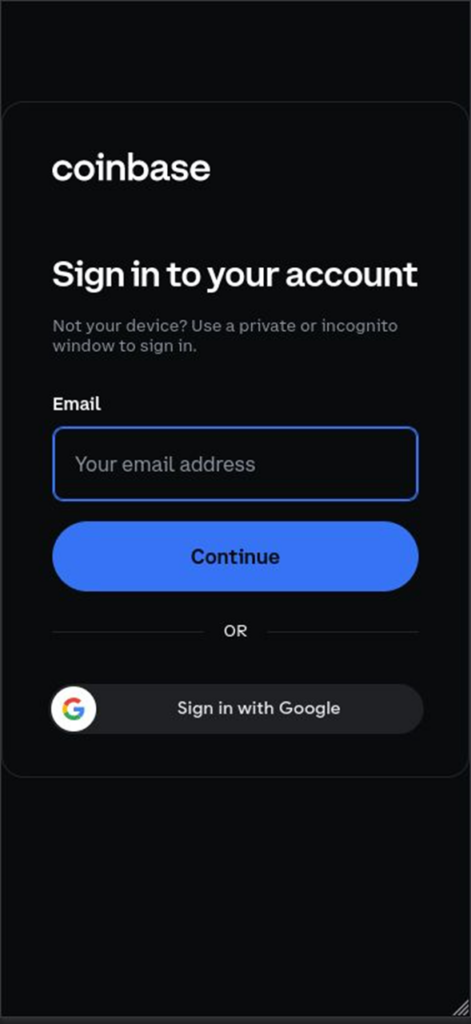
They particularly target users and staff members of cryptocurrency platforms, including Binance, Coinbase, Kraken, and Gemini. Their methods include creating fake login pages with the intention of stealing login credentials.
Attackers can use a multi-pronged social engineering phishing attack. They use emails, messages, and even phone calls (Vishing) to trick you into providing personal information on fraudulent websites. This may include usernames, passwords, or even your photo ID.
Lookout analysts discovered a recent phishing attack that is comparable to the Scattered Spider hacker group’s 2022 Oktapus attack. However, there is insufficient evidence to make a confident claim.
As noted by the researchers at Lookout:
It is unknown whether this is a single threat actor, or a common tool being used by many different groups. However, there are many similarities in the backend C2 [command-and-control] servers and test data our team found across the various phishing sites.
Uncovering the CryptoChameleon’s Deceptive Strategies
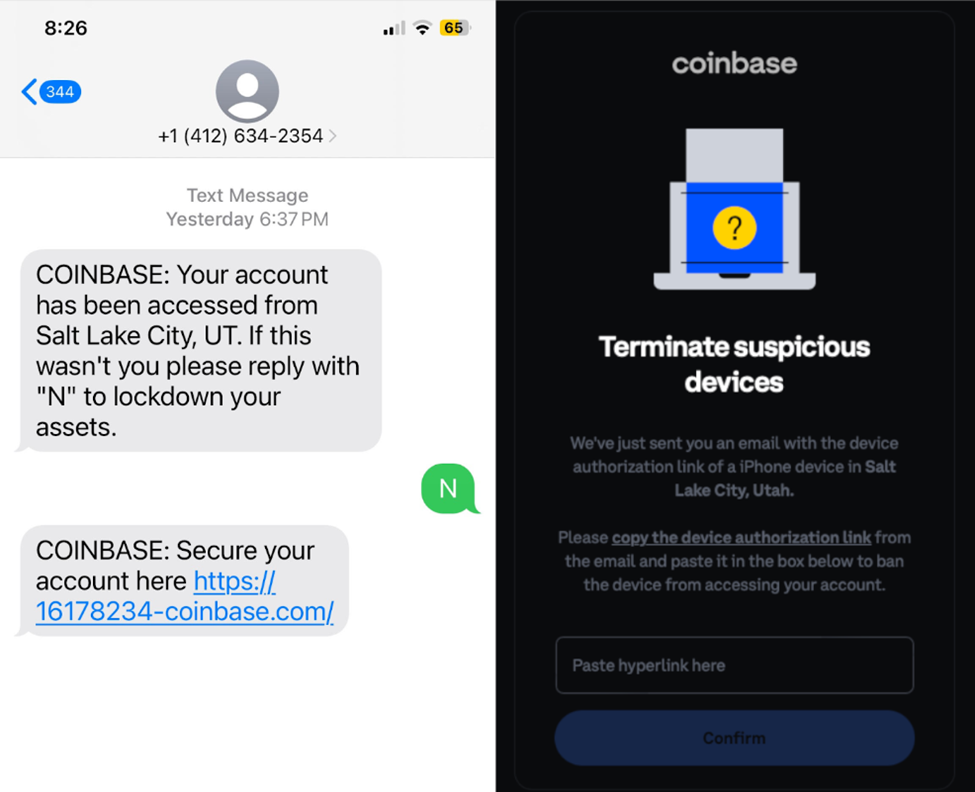
CryptoChameleon’s attackers employ advanced social engineering strategies, such as personalised SMS messages and phone calls. They aim to trick you into thinking they are professional support experts from trusted companies.
Phishing attackers frequently deceive users by spoofing trusted websites. They may, for example, register a domain name such as “fcc-okta[.]com,” which is almost the same as the official Okta login page created by the FCC with the exception of one character.
The attackers use a variety of communication techniques, faking customer service agents when they phone, email, or text the victim. This technique increases the complexity of these risky efforts by leading them to the phishing website under the assumption of account recovery.
The CryptoChameleon kit includes hCaptcha to help it avoid automated analysis tools. This novel approach prevents automated crawling and identification of phishing sites. Furthermore, since captchas are frequently connected to reliable websites, it might give people a misleading perception of authenticity.
After bypassing this anti-analysis security, the perpetrators send visitors to a carefully designed phishing website. The trick becomes more successful because this page precisely mimics Okta’s real login page.
The phishing kit used by hackers allows them to communicate with victims in real time. This simplifies incidents such as asking for further authentication, particularly when multi-factor authentication (MFA) codes are necessary to take over the target’s account.
Attackers may enhance fraud by customising fake websites using victim phone numbers within the central panel. After phishing, redirecting to genuine or fake websites reduces suspicion and allows more time for data exploitation.
Threat actors primarily hosted their phishing websites on Hostwinds and Hostinger in late 2023. They then switched to RetnNet, a hosting provider headquartered in Russia; nevertheless, this move could have prolonged the availability of suspicious websites.
Patrick Tiquet, Vice President of Security and Architecture at Keeper Security, highlights the need of multifactor authentication (MFA) in improving cybersecurity. Tiquet describes MFA as a critical second layer of defence, particularly useful in preventing phishing attacks.
However, he warns that attackers are constantly improving their strategies for bypassing MFA measures. Their expanding approaches represent a growing risk to high-value accounts, requiring people and organisations to be watchful and take proactive measures.
Phishing attacks are on the rise, and it is important to protect your organisation. One effective way to do this is by increasing user awareness about these types of attacks. Phishing Tackle is a great resource that can help you in this regard. They offer a free 14-day trial to help train your users to recognise and avoid phishing attacks.
Although technology can be helpful, it cannot spot 100% of phishing emails. Therefore, user education is important to minimising the impact of any successful attacks. Consulting with Phishing Tackle can provide valuable insights and tools to help you strengthen your defences against phishing attacks.