Hackers are using fake websites to gather information from journalists and government officials in Australia. These threat actors (TAs) use phishing emails to get victims to visit malicious websites that relate to Australian news organisations.
Content from BBC News was used to build the websites. After that, the hackers went after users to install malicious software on their devices, collecting their confidential data and selling it to Chinese hacker organisations.
Several sources claim that the hacking gang specifically targeted those working in the Asia-Pacific region’s wind-turbine manufacturing and alternative energy sectors. A US security company claimed that it was certain the hackers were working for the Chinese government.
Sherrod DeGrippo, vice president of Proofpoint Threat Research and Detection, said that the US Department of Justice agreed with them:
“We take attribution very seriously. We specifically don’t release attribution unless we have high confidence. The reason that we have such high confidence in this attribution really goes back to the DoJ formal accusation, which mentions these defendants and specifically calls out the Proofpoint name identifier of ‘Leviathan’.”
Who is responsible?
The UK’s National Cyber Security Centre stated in 2021 that it was “almost clear” the hackers were connected to the Chinese government, and Proofpoint said that the hackers were a part of a gang of which four members had been arrested by the US at the time.
According to Proofpoint:
A China-based, espionage-motivated threat actor that has been active since 2013, targeting a range of organisations in reaction to political trends in the Asia-Pacific area, with a focus on the South China Sea.
A request for information has been sent to the Australian Cyber Security Centre. In the most recent attack by the gang, victims reported receiving phishing emails claiming to be from someone who had launched a news website between April and June.
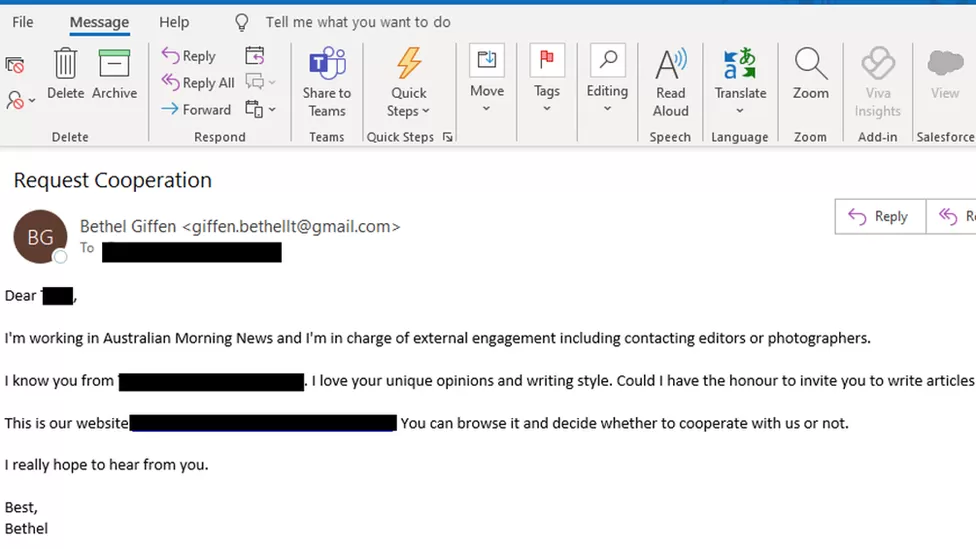
Attack Using Phishing Email
Hackers exploited reverse engineering to identify people connected to international politics and journalism in the most recent attack, which attracted headlines in Australia, the UK, China, and the US.
According to Ms DeGrippo:
What I find to be so innovative about it is that to look authentic, attackers even went as far as to develop these fake news sites by scanning actual websites, like the BBC. And further, they created multiple identities that they were sending from. There are around 50 of them. All the highly Anglo-styled names you could picture Australians having.
In order to reach their targets, the suspected hackers pretended to be legitimate news websites and sent emails to them. Since most fake websites were designed to seem like legitimate ones, it was clear that it invited journalists to study the site and consider writing pieces for them.
The fake website had malware that would attack the victim’s PC using a programme called Scanbox, which would check their profile, device, and web pages viewed.
Mitigation
The South China Sea offshore energy industry, who manufactures wind turbines and alternative energy, as well as defence contractors, persons working in the healthcare and financial services industries, appeared to be the target of the attack.
Ms DeGrippo said:
Typically, Chinese surveillance services do not pay much attention to users. However, anyone who has a sensitive role within their professional employment, even if they’re dealing with things such as engineering, things that might not seem like state secrets… the reality is China sees them as secrets and as important espionage information.
It is difficult to underestimate the importance of campaign volunteers or staff practising proper IT hygiene (such as using strong passwords and Multi-Factor Authentication) and avoiding discussing campaign material on personal email accounts at all costs.
Criminals who break into political parties look for harmful emails that were meant to be kept secret or unread. Making them public is a hacker’s method of doing as much harm as they can, especially damaging a party’s or individual’s credibility and reputation, and diverting attention from one subject to another.
Furthermore, Ms. DeGrippo added:
Professionally, organisations must consider the kind of data that their workers have access to and whether they have the right technology tools in place to protect their staff from these types of attacks.
Help your colleagues spot these phishing emails by starting your Phishing Tackle security awareness training today with our two-week free trial.