Europol engaged in a significant operation against the Ragnar Locker ransomware organisation in coordination with numerous foreign law enforcement agencies. As a result of this operation, the group’s main member was arrested in Paris. This ransomware group was behind a number of high-profile attacks on major networks throughout the world.
The operation, which lasted from October 16th to October 20th, 2023, included coordinated searches in Czechia, Spain, and Latvia. The “key suspect” involved with the ransomware was caught in Paris, France on October 16, 2023.
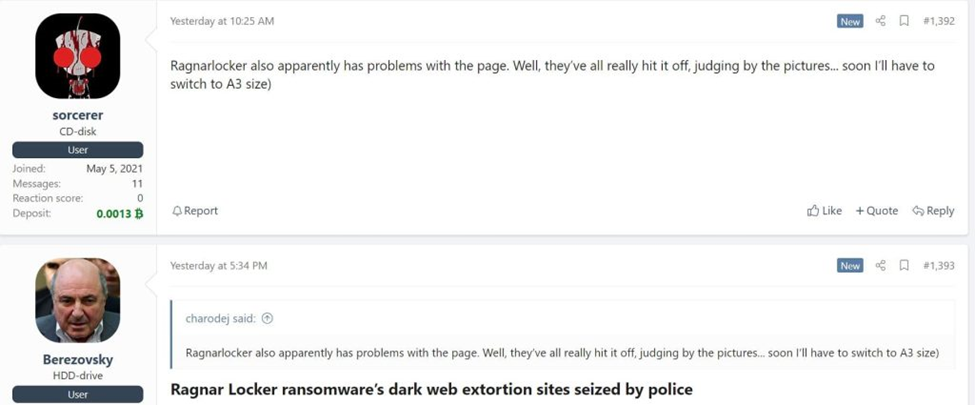
The ransomware system was also seized in the Netherlands, Germany, and Sweden, while the connected data leak website on Tor was taken down in Sweden. Two people connected to the ransomware group were previously arrested in Ukraine in 2021. A year later, another member was apprehended in Canada.
Investigators interviewed five individuals in Latvia and Spain following the operation. At the end of the operation, the Paris Judicial Court’s examining judges heard the case of the alleged founder of the Ragnar group.
Breaking the lid on Ragnar Locker Ransomware
Ragnar Locker, which first appeared in December 2019, is famous for a series of attacks on key infrastructure throughout the world. Since 2020, the group has attacked 168 international companies with cyberattacks, according to Eurojust.
This malicious actor created anonymity for itself by attacking key infrastructure across the world. Significant victims of the infamous Ragnar Locker ransomware group included Energias de Portugal (EDP), a significant Portuguese energy and power firm, and the well-known Japanese video game developer Capcom.
This ransomware outbreak was designed to penetrate systems running Microsoft Windows operating systems, and it often exploited accessible services such as Remote Desktop Protocol to gain system privileges.
One noted extortion technique used by the Ragnar Locker group was double extortion. In addition to demanding large sums of money for decryption software, they also wanted to stop the sensitive information they had taken from being made public. Because they frequently attacked vital infrastructure, they were considered to be a high threat.
In a direct warning to their victims, Ragnar Locker advised them not to contact law enforcement. According to information released by Europol, they threatened to publish all the stolen information from organisations that sought help on their dark web “Wall of Shame” leak site.
According to Ragnar Ransomware Group:
All that the FBI/ransomware negotiators/investigators do is muck things up, so we’re going to publish your stuff if you call for help.
However, law enforcement authorities such as the French Gendarmerie and the US FBI worked with Europol and INTERPOL. This collaboration resulted in the arrest of two active Ragnar Locker members in Ukraine in October 2021. The inquiry continued after that, leading to further arrests and disruptive activities.
Cybercrime experts completed two-week sprints and held fifteen coordination sessions to prepare for the most recent operations. They also provided support for crypto-tracing, malware analysis, and forensics. To facilitate seamless collaboration between all involved agencies, Europol established a virtual monitoring centre.
Cyber Police in Ukraine ran raids in Kyiv at a place connected to a suspected member, seizing electronic gadgets, computers, and cell phones. The Ukrainian Cyber Alliance (UCA) launched an intrusion and took down the Trigona ransomware group’s leak site concurrently with these activities.
Due to the shutdown of ten servers, UCA successfully extracted the data that was stored on them. There is convincing proof that the Trigona attackers used Atlassian Confluence for their illegal activities.
The Ragnar Locker ransomware group is the latest in a long line of cybercriminal organisations to face significant disruption. Authorities have effectively taken control of domains and dismantled the network components of multiple ransomware criminal groups, including Netwalker, Cl0P, DarkSide, REvil, and Egregor.
The US Justice Department launched a ‘months-long disruption’ operation against the Hive ransomware group. This cybercriminal group attacked over 1500 individuals in 80 countries. Since 2021, the Hive group has targeted hospitals, school districts, financial institutions, and key infrastructure, collecting ransom payments of more than $100 million.
The recent takedown of the Ragnar Locker ransomware organisation shows the importance of international collaboration in the investigation against cybercrime. Law enforcement agencies from numerous countries joined in this operation to effectively dismantle the group’s infrastructure and detain its top members. This joint effort shows the value of working together to handle unpredictable challenges caused by attackers.
Successful ransomware attacks are most often preceded by phishing emails. Help your colleagues keep a security-first mindset and boost your human firewall by starting your Phishing Tackle security awareness training today with our two-week free trial.