Security experts have uncovered phishing campaigns that abuse Cloudflare Workers to create fake login pages. These campaigns are designed to steal credentials for various services, including Microsoft accounts, Gmail, Yahoo!, and cPanel Webmail.
Netskope researcher Jan Michael Alcantara said in a report that the attack method, known as transparent phishing or adversary-in-the-middle (AitM) phishing, leverages Cloudflare Workers to function as a reverse proxy server. This scheme intercepts communication between the victim and an authentic login page, collecting credentials, cookies, and tokens.
Most phishing attacks hosted on Cloudflare Workers within the last 30 days have targeted victims in Southern Europe, North America, and Asia. The banking, financial services, and technology industries have been the main targets of these attacks.
According to a cybersecurity company, there was a significant surge in traffic to Cloudflare Workers-hosted phishing URLs during Q2 2023. The company saw a huge increase in the number of different domains, from little over 1,000 in Q4 2023 to almost 1,300 in Q1 2024.
Attackers Use Cloudflare Workers and HTML Smuggling for Phishing
Cloudflare Workers is a serverless computing technology that is good for deploying apps and delivering HTML pages. It is accessible to anyone on the free tier and is frequently used by attackers.
Attackers create many Cloudflare Worker apps, abusing these free services. They can use a publicly available domain and a valid TLS certificate to produce up to 100,000 accesses per day with a free account.
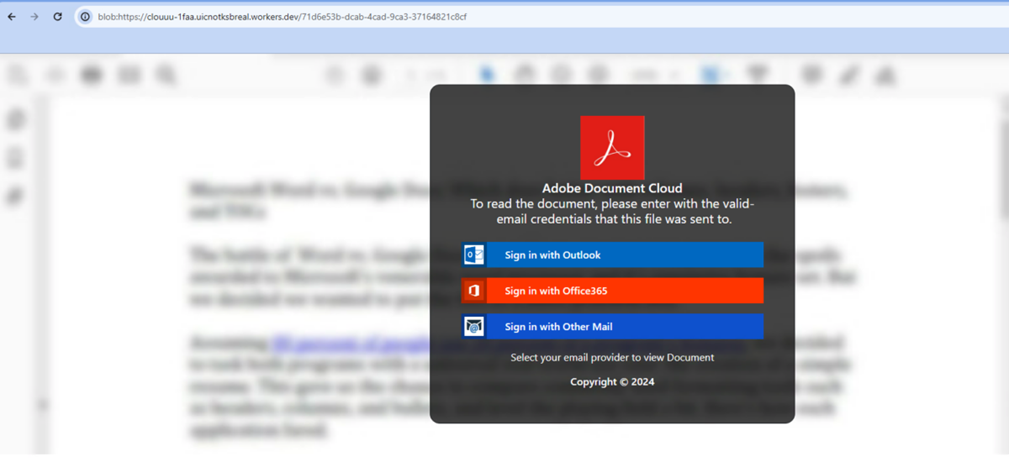
Delivering phishing pages using HTML smuggling is a common technique used in phishing campaigns hosted on Cloudflare Workers. HTML smuggling is a method for evading network restrictions by constructing disruptive payloads on the client side.
Malicious payloads are stored on the victim’s disc and then executed in these attacks. The phishing pages themselves serve as payloads, which the attacker rebuilds and shows in the browser.
The phishing page directs the user to sign in with Microsoft Outlook or Office 365 to view a fake PDF document. If users proceed, Cloudflare Workers capture their credentials and multi-factor authentication (MFA) codes through fake sign-in websites.
According to Michael Alcantara:
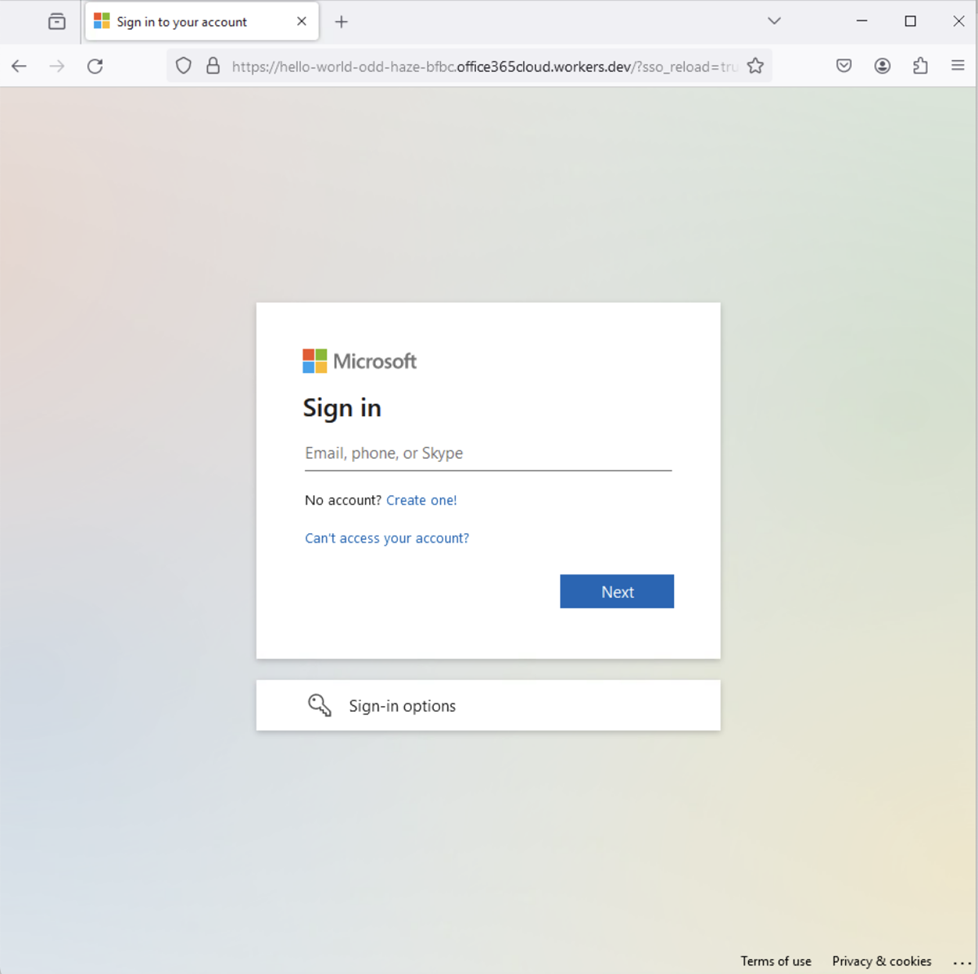
The entire phishing page is created using a modified version of an open-source Cloudflare AitM toolkit. Once the victim accesses the attacker’s login page, the attacker collects its web request metadata. Once the victim enters their credentials, they will be logged in to the legitimate website, and the attacker will collect the tokens and cookies in the response. Furthermore, the attacker will also have visibility into any additional activity the victim performs after login.
The phishing page is based on a modified open-source Cloudflare MITM toolset. The attacker builds a Cloudflare application with the “Hello World” Worker template. This template uses the addEventListener() function to listen for fetch events.
The attacker collects web request metadata, including HTTP request method, region, IP address, and headers, when the victim views the fake login page. Afterwards, the attacker sends the request on the victim’s behalf to the authorised website using this information.
Cybercriminals are always coming up with new ways to trick security systems. To avoid detection, they are employing generative artificial intelligence (GenAI) to create believable phishing emails and distribute large malware payloads—often more than 100 MB.
Moreover, threat actors are using GenAI to create deepfakes and build exploits, highlighting the necessity for strong security protocols, ethical standards, and oversight systems.
There is also a growing trend in creative ways to bypass standard detection systems. Domain Name System (DNS) tunneling is used by campaigns such as TrkCdn, SpamTracker, and SecShow to track targets’ opening of phishing emails and clicking on malicious links. In addition, these efforts monitor the delivery of spam and check victim networks for vulnerabilities.
Cybercriminal have also begun producing fake webpages that imitate financial companies such as Barclays. These pages provide real remote desktop software, such as AnyDesk, disguised as live chat help. This method gives them remote access to consumers’ systems.
Users who thoroughly inspect URLs can prevent becoming victims of attacks. Ensure you type the URL into your web browser to access significant websites, such as webmail or banking platforms. To defend against phishing schemes and other similar risks, organisations should regularly review their security procedures.
Phishing attacks are on the rise, and it is important to protect your organisation. One effective way to do this is by increasing user awareness about these types of attacks. Phishing Tackle is a great resource that can help you in this regard. They offer a free 14-day trial to help train your users to recognise and avoid phishing attacks.
Although technology can be helpful, it cannot spot 100% of phishing emails. Therefore, user education is important to minimising the impact of any successful attacks. Consulting with Phishing Tackle can provide valuable insights and tools to help you strengthen your defences against phishing attacks.