Money Message, a new ransomware group, has claimed responsibility for breaching the systems of Micro-Star International (MSI) Co. Ltd. The company has confirmed the breach and stated that the hackers stole source code from its internal network.
MSI is a renowned manufacturer of computer hardware and related items. Their range includes laptops, desktops, motherboards, graphics cards, industrial computers and peripherals.
The previous week, the Money Message ransomware group confirmed that they had hacked into some of MSI’s systems and taken files. These files will be released online if the company does not agree to pay a $4 million ransom.
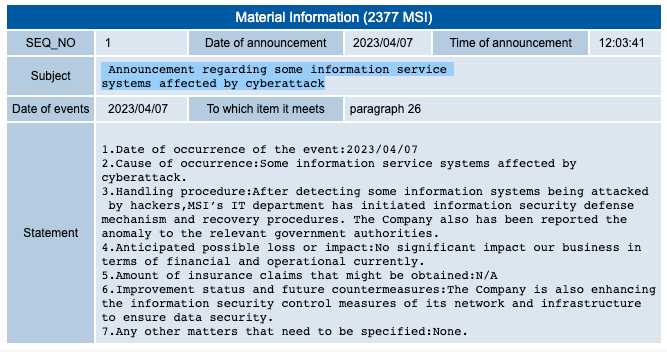
As observed by PCMag, MSI stated in a report with Taiwan’s Stock Exchange (TWSE) on Friday that a cyberattack had impacted some of its information service systems. The company also notified the appropriate authorities of the incident.
According to MSI:
After detecting some information systems being attacked by hackers, MSI’s IT department has initiated information security defense mechanism and recovery procedures. The Company also has been reported the anomaly to the relevant government authorities.”
The computer manufacturer did not disclose any information about the nature of the cyberattack it experienced and did not indicate whether any data was taken during the breach.
No significant impact our business in terms of financial and operational currently. The Company is also enhancing the information security control measures of its network and infrastructure to ensure data security.
MSI has issued a new statement advising users to avoid downloading firmware and BIOS updates from third-party sources. Instead, they should obtain such software exclusively from the company’s official website.
MSI’s notification was released just a few days after a ransomware group named Money Message announced on its leak site that it had hacked into the company’s infrastructure. The group also displayed screenshots of files allegedly containing software source code, private keys, and BIOS firmware.
Recovering from Money Message Group’s Attack
MSI has confirmed that the affected systems are now back to normal operations. The company has also stated that there have been no major financial impacts from the cyberattack. This update reassures stakeholders of MSI’s ability to withstand difficult circumstances.
ThreatLabz tweeted about the Money Message ransomware group’s potential involvement in breaching a major computer hardware vendor. They had previously shared information about the group’s operations.
MSI said it will be implementing stricter security measures throughout its network and infrastructure in a statement with the Taiwan Stock Exchange. The business recognises the value of securing sensitive information and protecting data. These steps aim to improve the security and privacy of their systems.
In a conversation between an MSI representative and the Money Message ransomware group, the group claimed to have stolen about 1.5 terabytes of documents from MSI’s network. They also demanded a ransom of $4 million from the company.
Money Message uses a double ransom strategy, first stealing the victim’s data and then encrypting it. The gang then uploads the stolen data to its leak site in the situation that the ransom is not paid.
The ransomware attack on MSI highlights the need for strong cybersecurity practices in a world that is becoming increasingly digital. As the company recovers from the attack and strengthens its security measures, the incident serves as a reminder of the importance of taking proactive steps to protect against cyber threats.
Both organisations and individual users must be careful by remaining aware of possible risks. They should also follow best practices to protect their data and systems.
Successful ransomware attacks are most often preceded by phishing emails. Help your colleagues keep a security-first mindset and boost your human firewall by starting your Phishing Tackle security awareness training today with our two-week free trial.