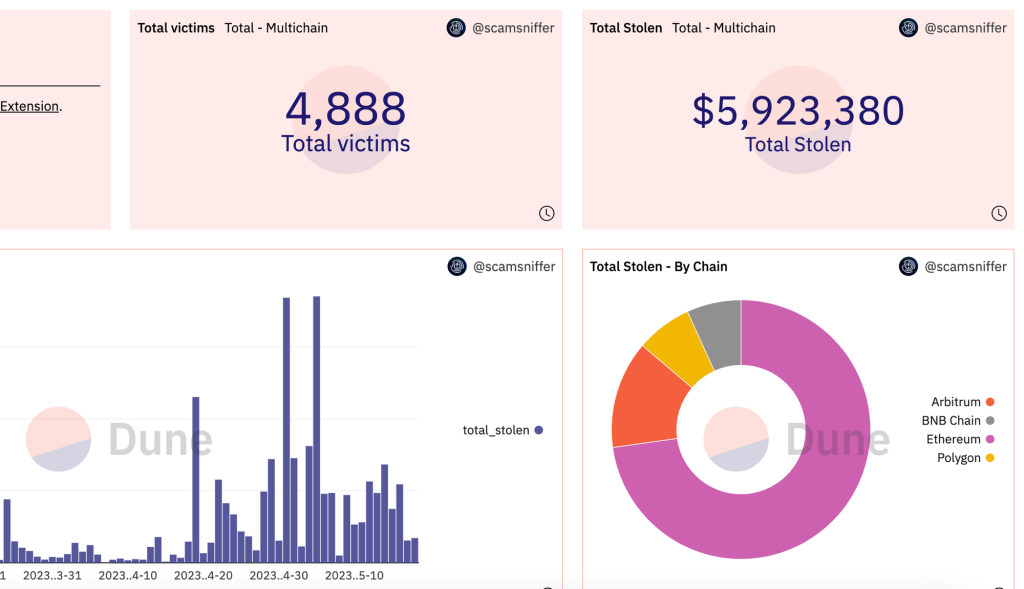
Inferno Drainer, a business infamous for Bitcoin phishing and fraud, is said to have scammed approximately $5.95 million from 4,888 victims. They are largely focused on the larger blockchains, mostly those hosting your favourite crypto projects.
A website that focuses on exposing scams, Scam Sniffer, announced last week that the malicious software vendor is allegedly connected to hundreds of schemes that resulted in the theft of several million dollars. Since March 27, 2023, the phishing service has created at least 689 fake websites.
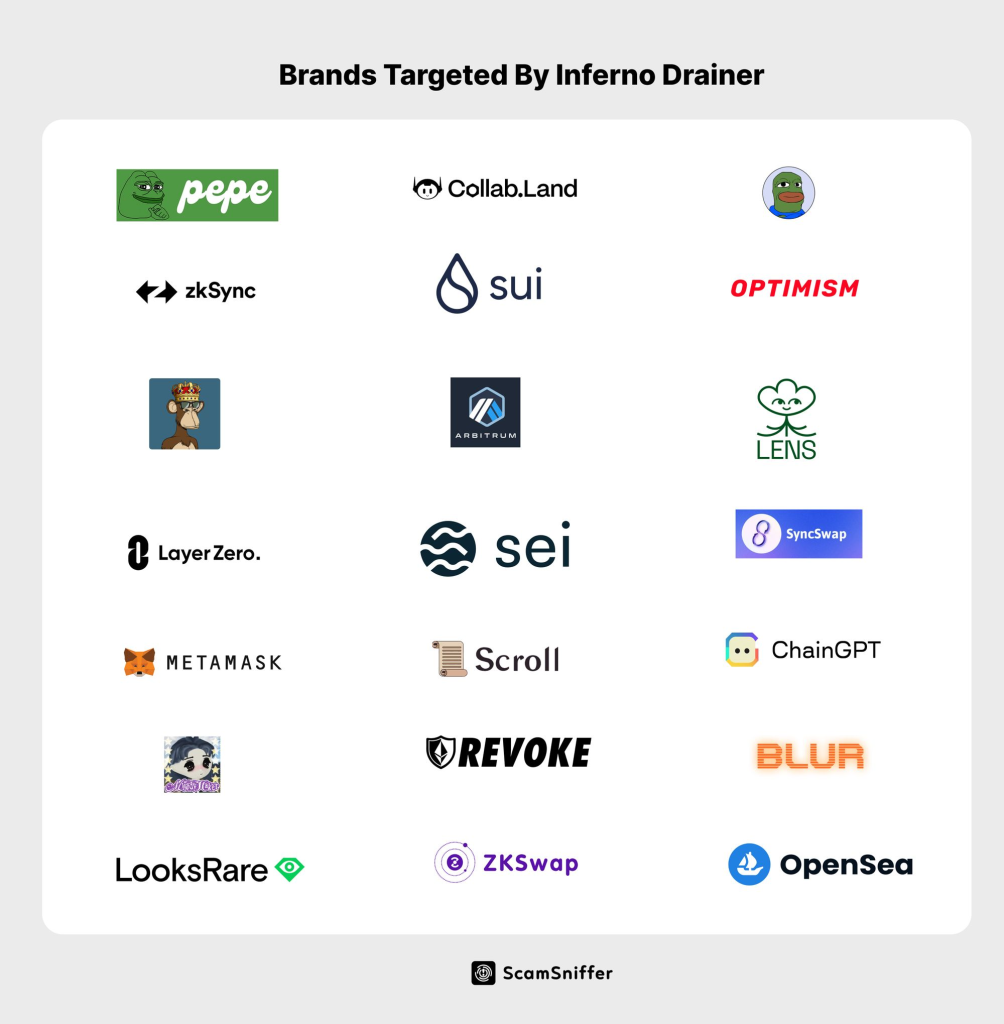
Analysts who followed an increase in site-creation activity around that time reported that around May 14th, 2023, there was a noticeable rise in the number of phishing sites going live. These malicious websites, which have 229 well-known brands as their targets, were created using Inferno Drainer. Pepe, Bob, MetaMask, OpenSea, Collab.Land and LayerZero are a few examples of these.
Cryptocurrency frauds continue to be common during a falling market. A recent analysis by Crystal Blockchain found that 2022 was the worst year ever for Bitcoin fraud, with a total of 120 unique incidents documented.
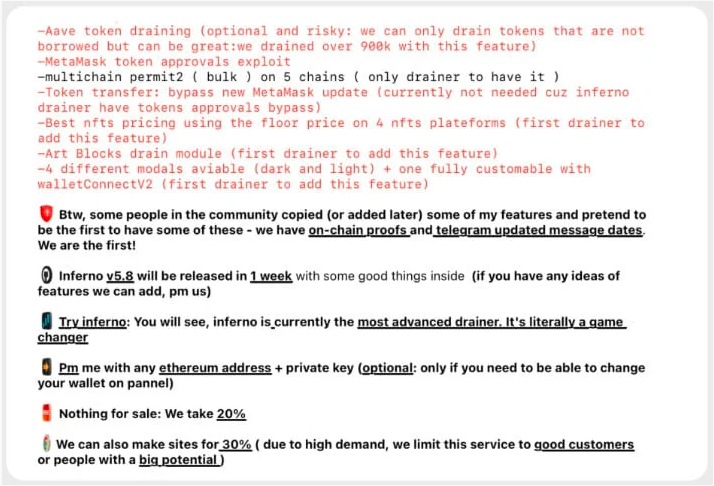
The importance of these fraudulent operations became widely known after an alleged member of Inferno Drainer, identified as “Mr Inferno,” managed to infiltrate the Scam Sniffer Telegram channel. This hack led to the discovery of a website that promotes the scammer’s services. Furthermore, Mr. Inferno demonstrated the expertise by releasing a screenshot of a $103,000 heist on Telegram.
According to Scam Sniffer:
By querying the transaction hash obscured in the screenshot, we found this transaction in ScamSniffer’s database and associated it with some known malicious addresses in our malicious address database.
According to sources, Inferno Drainer allegedly earns money by charging a 20% to 30% charge on illegally obtained assets as payment for their destructive software. Approximately 689 phishing websites have reportedly been launched by Inferno Drainer since March 27. But according to Scam Sniffer, the on-chain activity suggests that the activities may have started earlier than this date.
Crypto Brands Threatened by Malware-as-a-Service
As a “malware-as-a-service” platform, Inferno Drainer provides the malicious software and website hosting in exchange for a percentage of the money that has been taken.
The victim’s worst financial loss came to around $400,000. The victim advised that the con artist keep 50% of the stolen things to recover some of the stolen property.
Venom Drainer, which was able to steal $27 million from around 15,000 people. Surprisingly, the five worst-affected individuals collectively lost $14 million. Due to the high demand, the firm will only offer phishing sites to “valued customers” or people who have proven that they can make significant money.
Crypto scams are on the rise
The majority of the money, $4.3 million worth, was obtained illegally through the Mainnet. The theft of $5.9 million came from a combination of $790k from Arbitrum, $410k from Polygon, and $390k from BNB.
The analysts’ largest victims included one who lost £400,000 worth of assets. The victim then got in contact with the attackers, offering to pay them 50% of the total sum in exchange for their not being charged with a crime. The victims received no response from the attackers.
Analysing the on-chain money collecting accounts shows an estimated total of 1,699 Ethereum was stolen and distributed across these five important addresses. Notably, the attackers make sure that each address’s balance is intentionally kept between 300 and 400 ETH.
Cryptocurrency holders should use caution in all transactions. It is important that they treat incoming messages with sceptical thinking, verify the sender’s identity, use multi-factor authentication to protect their accounts, and keep their software up to date. It is preferable to avoid sharing any personal information on the internet and instead keep most of one’s digital assets safely using hardware cold wallets.
Phishing Tackle offers a free 14-day trial to help train your users to avoid these types of attacks and test their knowledge with simulated attacks using various attack vectors. By focusing on training your users to spot these types of attacks, rather than relying solely on technology (none of which can spot 100% of phishing emails), you can ensure that your organisation is better prepared to defend against cyber threats and minimise the impact of any successful attacks.