Google Play enables the developer community to deliver the most creative and trusted apps to billions of users around the world. It has made numerous policy changes for Android app developers that will improve user, Google Play, and app security.
Google Play collaborates with developers to ensure that their applications run seamlessly on newer Android versions, ensuring that users get the full advantages of these advancements while maintaining the trusted experience that customers expect.
A new update has been announced that will be available between May 11th and November 1st, 2022, providing developers enough time to adjust to the latest changes.
The following are the most major cybersecurity and fraud policy changes:
- Targeted criteria for API level
- Apps with an Annual Percentage Rate (APR) of 36% or above will be rejected.
- Prohibiting the Exploitation/Misuse of the Accessibility API.
- Permission to install packages from external sources now has a new policy.
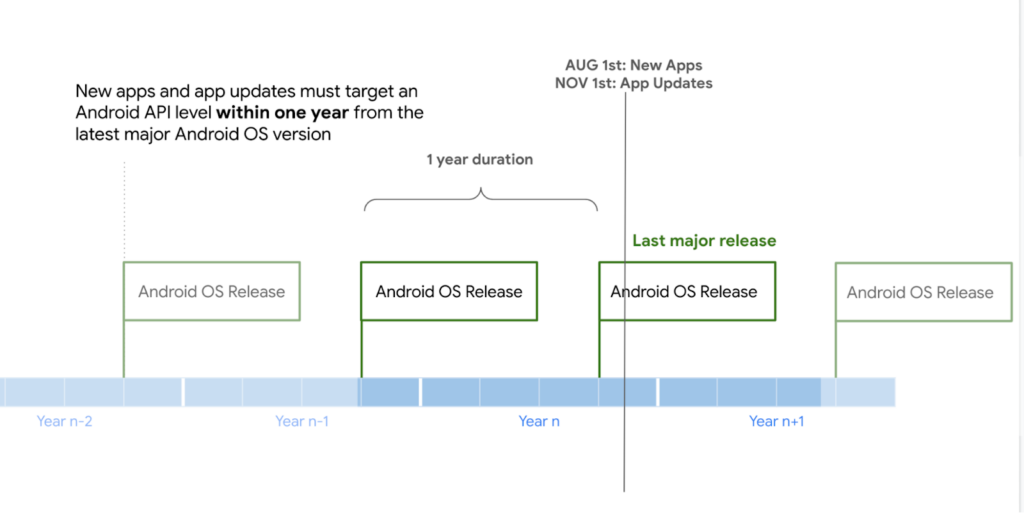
Targeted criteria for API level
Google now demands that new apps and app updates target an Android API level within a year of the release of the most recent version of the Android OS. Apps that fail to meet these criteria will be withdrawn from the store. These changes will go into effect on November 1, 2022.
Existing applications that do not target the API level within two years of the most recent major version of Android will be removed from the Play Store and will not be discoverable or installable for new users with devices running Android OS versions higher than the apps’ target API level.
Also, the required requirement will vary when new Android OS versions are released in the future.
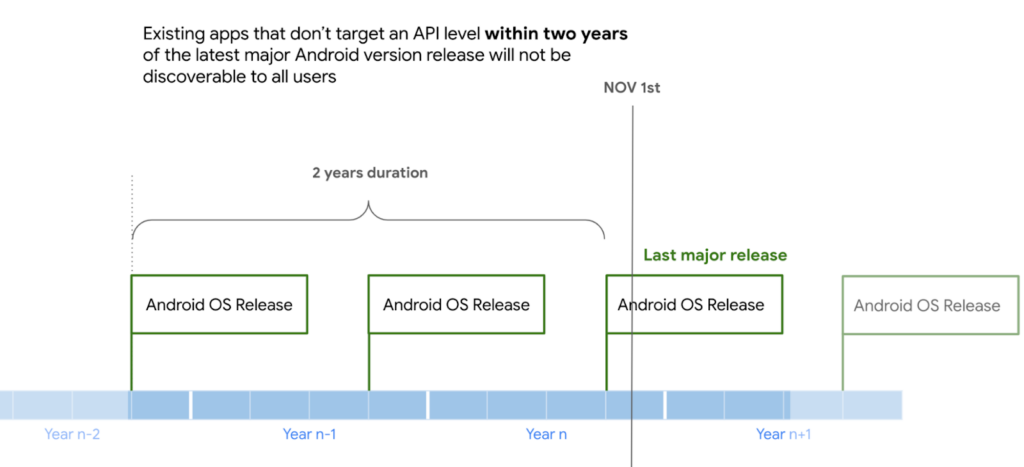
API level targeting requirements are required from November 1, 2022 (Google)
This update aims to force app developers to follow the tougher API policies that underpin later Android versions, such as better permission management and revocation, notification anti-hijacking, knowledge privacy upgrades, phishing detection, splash display limits, and so on.
“Users using the most updated devices, or those who are fully up to date on Android upgrades, may expect to get the most out of all of Android’s privacy and security features.”
Google’s new policy
App developers that need more time to move to more recent API levels can seek a six-month extension, however this is not guaranteed for everyone.
This policy change is expected to force many older applications to adopt safer methods, but it may also compel a lot of non-actively produced apps to leave the Play Store. One side effect of the latter may be people looking for an APK of their favourite software from unknown sources, and it could be infected with malware.
Misuse of the accessibility system API
The Android Accessibility API allows developers to create apps for people with disabilities, providing for new methods to control the device and use its apps. This feature, however, is frequently misused by malware to conduct tasks on an Android smartphone without the user’s permission or even awareness.
Google’s new policy enhanced safety imposes additional limits on how this coverage can be used, as indicated below.
- Change user settings without their permission or restrict users from disabling or uninstalling any app or service unless approved by a parent or guardian via a parental control app, or authorised administrators via enterprise management software.
- Change or exploit the user interface in a misleading manner or in any other way that violates Google Play Developer Policies.
- Use Android’s built-in privacy and notification controls.
Package retrieval policy
Google has also announced a significant policy change that prioritises the “REQUEST INSTALL PACKAGES” permission.
To get their app approved on the Play Store, malicious developers hide package-fetching functionality, which downloads malicious packages after installation.
Users perceive these activities as an “update request” or “download latest content,” and either agree to the activity when the appropriate prompt appears, or they don’t see anything because it’s happening in the background. Google wants to close this gap by implementing new permission restrictions, bringing attention to an area that was formerly uncontrolled.
Allowed functions will be restricted to web browser, search, connect, file sharing, file transfer, file management, and business device administration. Apps that use this permission should now only fetch digitally signed packages, as self-updates, code alterations, and building APKs in the root file are no longer permitted.
Developers who want to ensure that their apps continue to appear in the Play Store will need to update their apps on a regular basis to target newer Android versions.
Has your organisation started to increase cyber security measures yet? Start your two-week free trial today.