Fenix cybercrime group has targeted tax-paying citizens in Mexico and Chile. They lure victims to phishing sites that look like the official sites of Mexico’s Servicio de Administración Tributaria (SAT) and Chile’s Servicio de Impuestos Internos (SII), allowing them to access sensitive information.
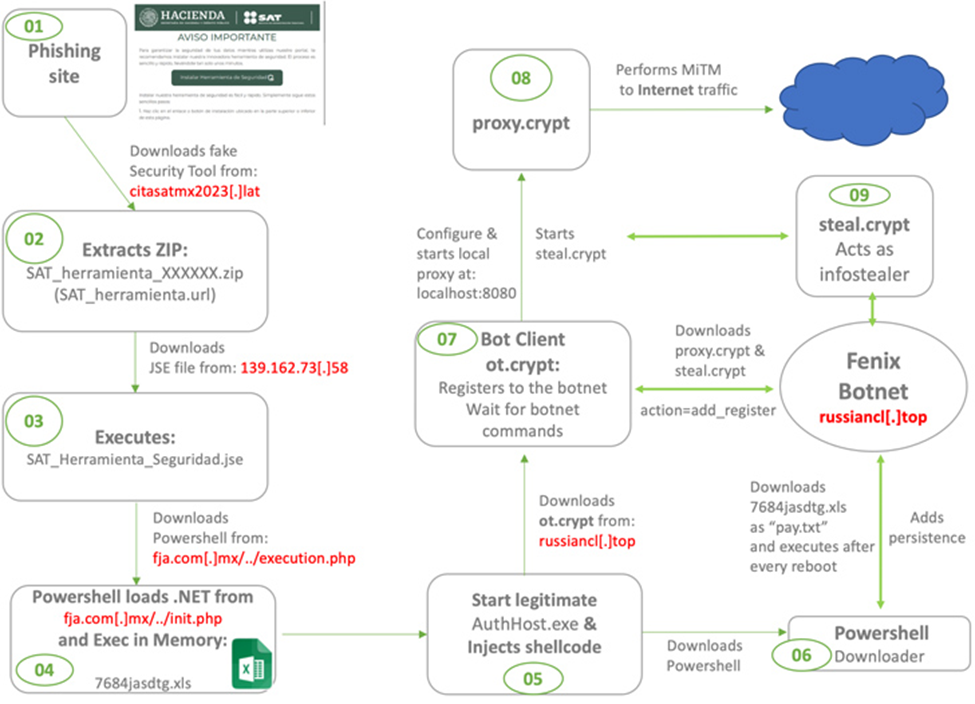
Such phishing sites suggest customers download a fake security program and claim that doing so would increase the security of their portal access. Although the victims are unaware of it, this download instals the initial layer of malware, making it possible for sensitive data, including credentials, to be stolen in a future attack.
According to the cybersecurity firm, with a particular focus on Chile and Mexico, Fenix intends to function as an initial access broker and gain access to numerous businesses in the area. In order to earn more money, it then goes on to offer this access to ransomware associates.
The information gained thus far suggests that the threat actor has been arranging phishing attacks to coincide with government events for at least a year, beginning in the fourth quarter of 2022.
Visitors are urged to download software that claims to secure personal data while using the spoof websites. Phishing websites that encourage users to download authentic programmes like AnyDesk are used to trick users.
“Fenix compromises weak websites using vulnerable WordPress engines and also creates new domains to launch phishing campaigns, creates typosquatting domains similar to known apps like AnyDesk, WhatsApp, etc.”.
A malicious process is started by the ZIP file that contains the programme. A hidden PowerShell script that loads and runs a.NET binary is activated by this series of events. Then, to trick the user, a notice with the Spanish phrase “Ahora se encuentra protegido,” which translates to “Now you are protected,” displays.
After the execution of the programme instals the framework for attaining persistence on the compromised host. It then deploys botnet malware capable of executing orders from a remote server. Additionally, it launches a stealer module meant to retrieve credentials saved in online browsers and crypto wallets, concluding in its self-deletion.
Businesses typically get attacked with ransomware because of unintentional employee behaviour. This usually occurs when an employee falls victim to a phishing scam, clicks on a risky URL, or downloads and opens a malicious file. Conducting cybersecurity awareness and education courses for all workers, partners, and stakeholders is important. Regularly offer consistent and up-to-date advice. Employees who are unprepared might expose the business to severe risks. Make sure that the staff is aware of what to do in the event of a ransomware and phishing attack and alert management of any such events as soon as possible.
Phishing Tackle offers a free 14-day trial to help train your users to avoid these types of attacks and test their knowledge with simulated attacks using various attack vectors. By focusing on training your users to spot these types of attacks, rather than relying solely on technology, you can ensure that your organisation is better prepared to defend against cyber threats and minimise the impact of any successful attacks.