Researchers are referring to the BlackByte ransomware group’s latest approach as “Bring Your Own Vulnerable Driver” (BYOVD). By disabling more than 1,000 drivers used by security solutions, this strategy makes it possible to bypass firewalls.
BYOVD is an attack approach in which threat actors take advantage of vulnerabilities in authentic, signed drivers to successfully exploit kernel-mode and grab control of vulnerable systems. Lazarus’s use of a misconfigured Dell driver and an unidentified hacker’s exploitation of a Genshin Impact game’s anti-cheat driver/module are two significant examples of BYOVD attacks002E
According to a recent technical article by Sophos, security expert Andreas Klopsch:
The deception approach enables deactivating a massive list of over 1,000 drivers on which security companies rely to give protection.
This group has been involved for recent attacks using a version of the MSI Afterburner RTCore64.sys driver, which is open to a privilege escalation and code execution bug listed as CVE-2019-16098.
BlackByte ransomware exploited the security flaw to deactivate drivers that limit the working of several endpoint detection and response (EDR) and antivirus programmes. Because the vulnerable drivers are signed with an authentic certificate and work with high privileges on the system, the “Bring Your Own Vulnerable Driver” (BYOVD) technique is successful.
How does BlackByte ransomware work?
The misconfigured MSI graphics driver provides I/O control codes that are visible by user-mode programmes, according to security experts at the cybersecurity firm Sophos. It goes against Microsoft’s security policies on access to kernel memory.
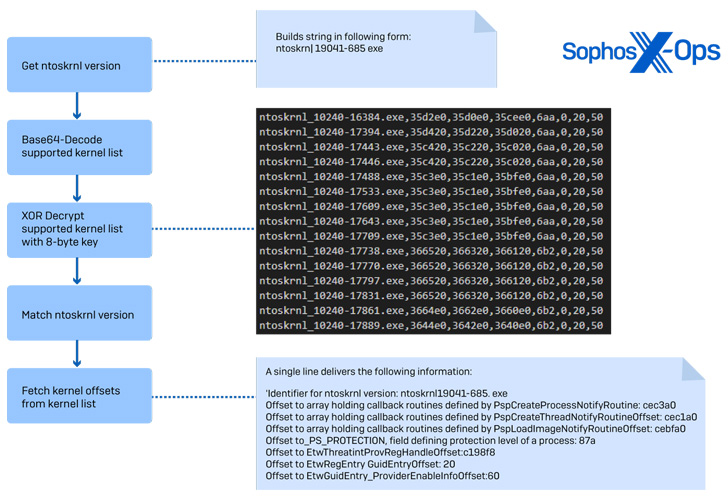
This enables hackers to access kernel memory without the need for shellcode or an exploit to view, execute, or perform operations there. To select the right sectors that match the kernel ID, BlackByte ransomware first detects the version of the kernel.
BlackByte continues by adding RTCore64.sys in the AppDataRoaming folder after finding the offsets and the kernel version. The filename is not included in the file extension since it is context sensitive into the binary.
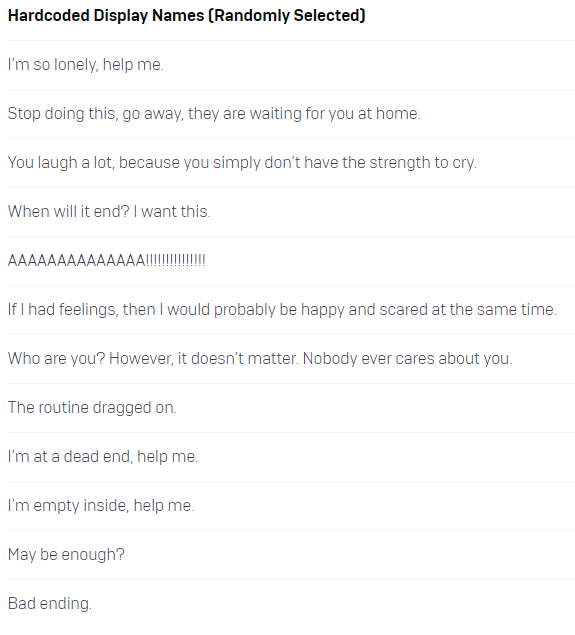
By using CreateServiceW, a service is built and then launched. Both the service name and the display name are cached into the binary. Although the display name is always chosen at random from a collection of highly unpleasant strings, the service name remains constant.
The attackers then take advantage of the driver’s vulnerability to remove Kernel Notify Routines related to security tool services. A list of 1,000 targeted drivers that enable the operation of AV/EDR tools is compared to the call-back addresses that are accessed to find the name of the matching driver.
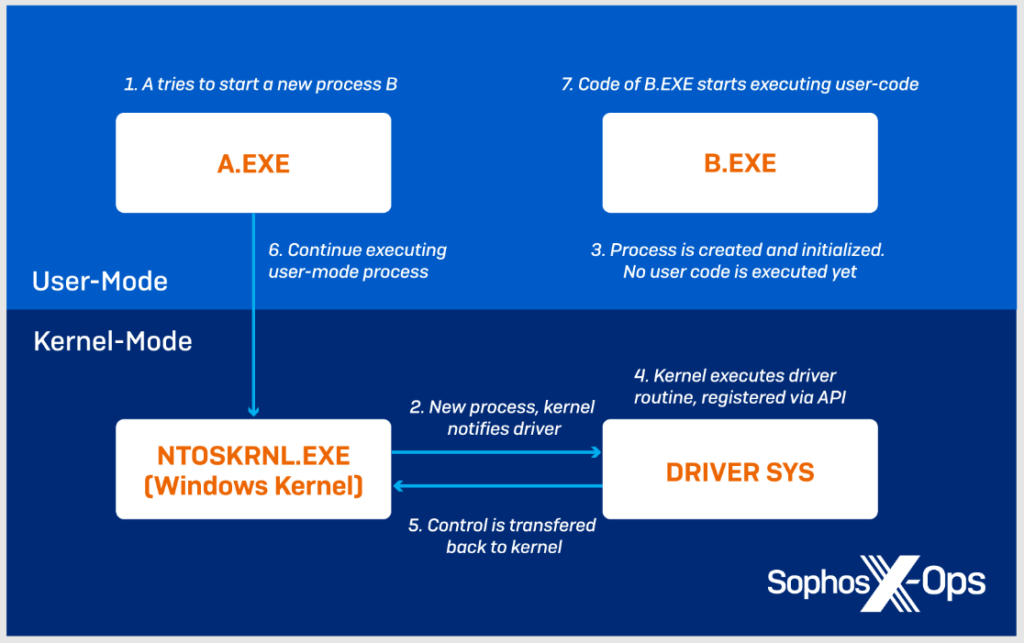
The kernel will transfer control and run the registered driver call-back function if a response has been requested by a driver using PsSetCreateProcessNotifyRoutine. When the driver procedure is complete, control is returned to the kernel, allowing the user-mode code to continue.
The part that has the location of the call-back function is overwritten with zeros to null the targeted driver and erase any matches discovered during this step.
In addition, BlackByte uses a number of techniques, such as checking for signals that a debugger is running on the target machine before exiting, to avoid being caught by security researchers. These techniques are identified by Sophos.
BlackByte ransomware scans for a list of capturing DLLs used by Comodo Internet Security, Windows DbgHelp Library, Sandboxie, and Avast. If any are discovered, the malware stops running. By adding the specific MSI driver to an updated blocklist, system administrators can prevent against BlackByte’s latest security bypassing approach.
Always keep an eye on and update the drivers that are installed on your PCs. Administrators should keep an eye on every driver installation event and examine it carefully to spot any unauthorised uploads that don’t match the hardware.
Help your colleagues keep a security-first mindset and boost your human firewall by starting your Phishing Tackle security awareness training today with our two-week free trial.